Loading blog post...
Protecting Sensitive Data on Blockchain Using Encryption and Zero-Knowledge Proofs
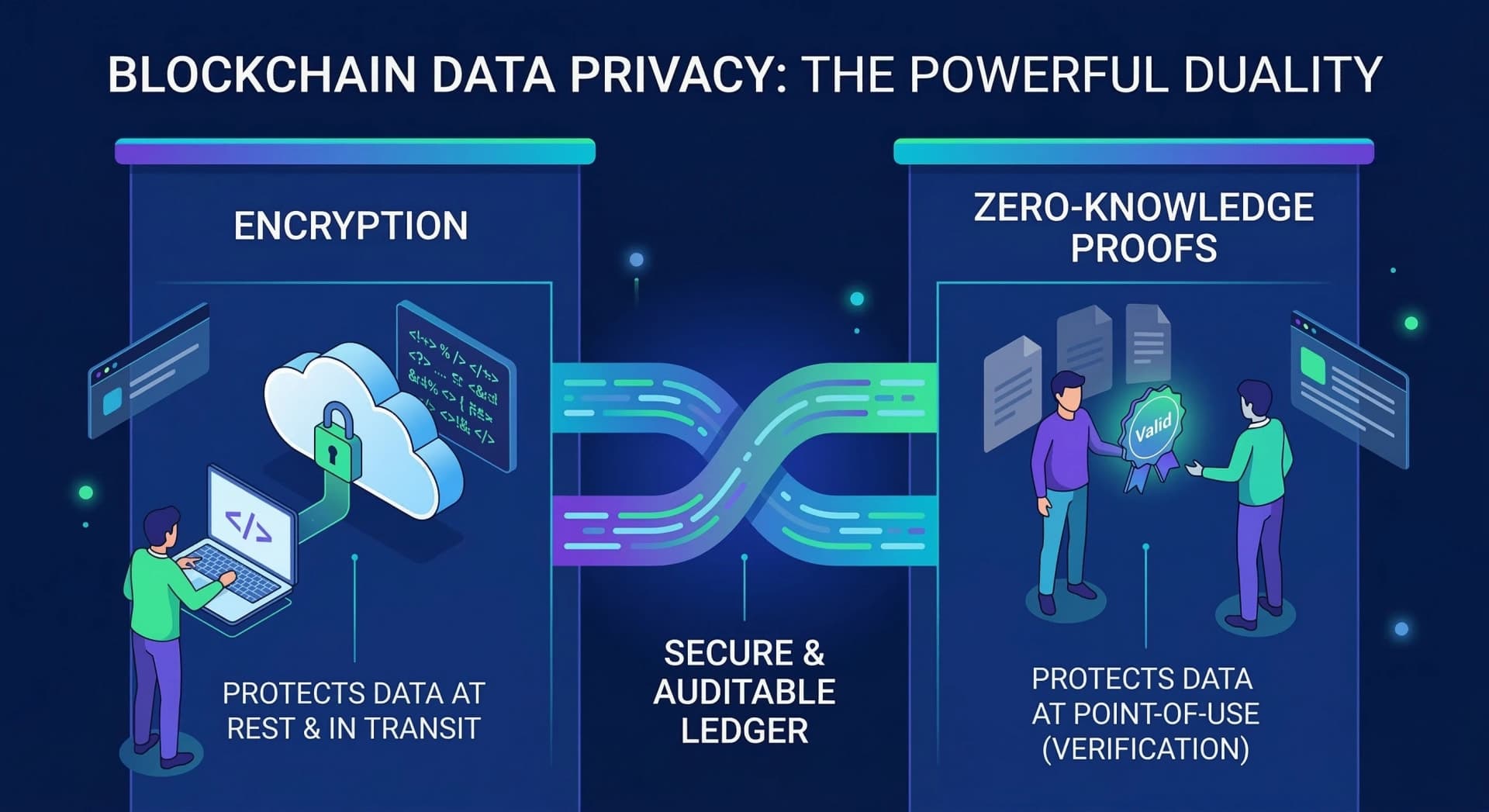
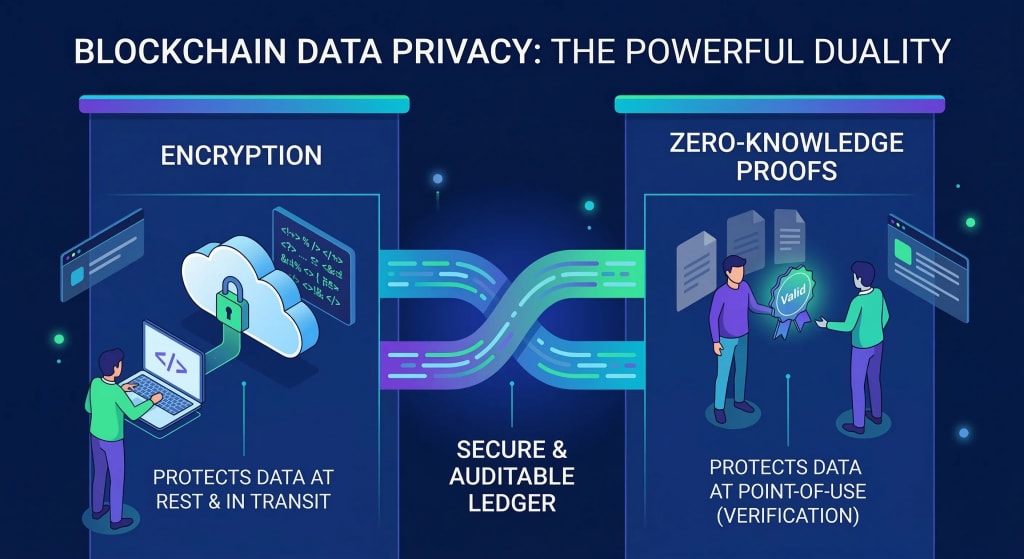
Blockchain transparency is a double-edged sword. While it ensures accountability, it leaves sensitive data like healthcare records and financial positions exposed. This guide explores how the powerful combination of encryption at the data layer and Zero-Knowledge Proofs (ZKPs) creates a "verifiable privacy" model, allowing you to prove the truth of your data without ever revealing the data itself.
Blockchain's core promise is transparency. Every transaction recorded, every state change visible, every participant accountable. That transparency is also its most uncomfortable property when sensitive data is involved.
Healthcare records, financial positions, identity credentials, voting choices, all these are things people need to prove without exposing. And the default model of putting everything on a public crypto ledger does not accommodate that need gracefully.
Zero knowledge proofs are the most technically significant answer the space has produced. Combined with encryption at the data layer, they allow blockchain systems to be both verifiable and private which turns out to be a harder problem than it sounds, and a more important one than most people realize.
Why Blockchain Data Privacy Is Harder Than It Looks
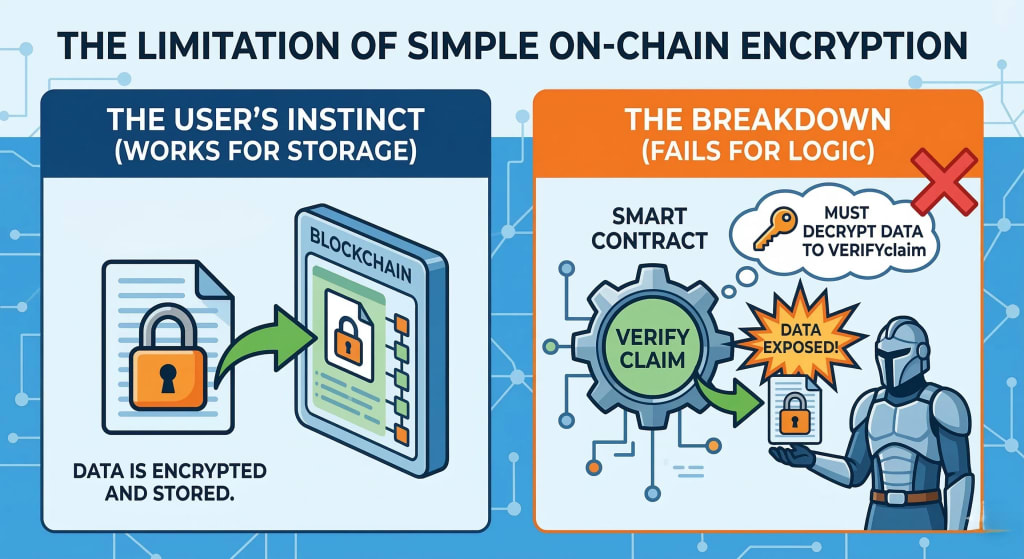
The instinct when people first encounter blockchain data exposure is to say: just encrypt it. Store the encrypted version on-chain, keep the key off-chain, problem solved.
This works for simple storage. It breaks down almost immediately for anything more complex.
If a blockchain application needs to verify a claim about encrypted data, that is confirm that a transaction is valid, that a balance is sufficient, that a credential is authentic, it typically needs to decrypt the data to check it. Which means the data is exposed at the point of verification. The encryption protected it in transit and at rest, but not at the moment it mattered.
This is the gap that zero knowledge proofs fill. They allow one party to prove to another that a statement about data is true without revealing the data itself. The verifier learns that the claim is valid. They learn nothing else.
For blockchain for data privacy specifically, this is transformative. It means the verification that the network needs to function can happen without the underlying sensitive information ever being exposed on-chain.
Zero Knowledge Proofs: What They Actually Do
A ZKP is a cryptographic protocol between a prover and a verifier. The prover knows something - a private key, a balance, an identity credential. The verifier needs to confirm that the prover knows it, without learning what it is.
The classic illustration: proving you know a password without typing the password. More practically relevant for blockchain: proving a blockchain transaction is valid without revealing the sender, receiver or amount.
ZK proofs achieve this through mathematical constructions that allow the prover to generate a proof, a compact piece of data that the verifier can check against public parameters. If the proof verifies, the statement is true. If it doesn't, it isn't. The private inputs that generated the proof remain private throughout.
The two most practically relevant variants in blockchain contexts are:
- zk-SNARKs — Non-interactive Arguments of Knowledge. Small proofs, fast verification but require a trusted setup ceremony to generate the public parameters. Used in Zcash, early zkEVMs.
- zk-STARKs — Scalable Transparent Arguments of Knowledge. Larger proofs but no trusted setup required, and post-quantum secure. Used in StarkNet and increasingly in data integrity applications.
The choice between them involves tradeoffs in proof size, verification speed and trust assumptions, decisions that matter when designing systems where blockchain transaction throughput and cost are constraints.
If you're evaluating which ZK construction fits your protocol's requirements, our Blockchain Development Services includes technical scoping for teams building privacy-preserving applications.
Zero Knowledge Proof in Blockchain: Where It's Actually Being Used
Zero knowledge proof in blockchain has moved well past theoretical interest. Several live systems are using it to solve real privacy problems today.
- Private financial transactions — Zcash pioneered the use of ZKP for shielded transactions, where sender, receiver, and amount are all hidden on a public crypto ledger while the network still verifies no double-spend occurred. More recently, protocols like Aztec have brought programmable privacy to Ethereum, allowing confidential smart contract execution.
- Identity and credential verification — Instead of submitting a passport scan or a bank statement to verify eligibility, a user can submit a zk proof that they meet the criteria over 18, accredited investor, resident of a specific jurisdiction — without revealing the underlying document. The verifier learns only that the claim is valid.
- Scalability via ZK rollups — This is currently the highest-volume application of ZKP in production. ZK rollups batch thousands of transactions off-chain, generate a proof that all of them are valid, and post only that proof to the main blockchain. The result is drastically lower costs and higher throughput, with the same security guarantees as the base layer. StarkNet, zkSync, and Polygon zkEVM are all live implementations.
- Compliance without exposure — Financial institutions experimenting with blockchain for data reporting can use zk proofs to demonstrate regulatory compliance, proving reserve adequacy, transaction limits, counterparty eligibility without publishing the underlying blockchain data that competitors or adversaries could exploit.
How Encryption and ZK Proofs Work Together at the Data Layer
Zero knowledge proofs and encryption solve adjacent but distinct problems, and the most robust privacy architectures use both.
Encryption protects data at rest and in transit, it prevents unauthorized parties from reading blockchain data they shouldn't see. ZK proofs protect data at the point of use, they allow computation and verification to happen over encrypted data without decryption.
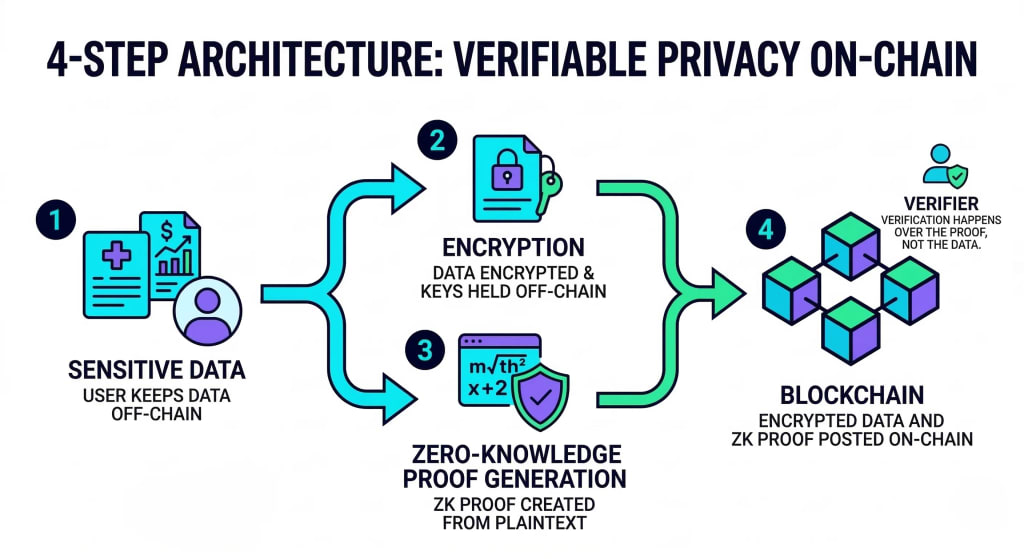
In a well-designed system, the layers work like this:
- Sensitive data is encrypted before it touches the blockchain, using keys controlled by the data owner
- A ZKP is generated over the plaintext data before encryption, proving whatever property the network needs to verify
- The proof and the encrypted data are posted on-chain
- Verifiers check the proof, confirming validity without ever accessing or needing the plaintext
The crypto ledger records the proof and the ciphertext. The network gains the verification it needs. The sensitive data never appears in readable form anywhere on-chain.
This architecture is particularly relevant for healthcare, where patient data needs to remain private but treatment records or insurance eligibility need to be verifiable. It applies equally to legal contracts, voting systems, and any context where "prove this is true without showing me the evidence" is a legitimate requirement.
Blockchain Wallets and the Privacy of On-Chain Identity
One of the most underappreciated privacy problems in blockchain is how much a blockchain wallet reveals about its owner not through any breach, but simply through the transparency of the ledger.
Every blockchain transaction a wallet sends or receives is permanently visible to anyone who looks. With enough transaction history, it is often possible to infer:
- The approximate financial position of a digital wallet crypto address
- Regular transaction counterparties, suggesting business relationships
- Behavioral patterns that correlate to identity even without a name attached
For top crypto wallets that have been used for years across many applications, this data trail is substantial. Blockchain analytics firms make their business from exactly this kind of inference.
ZK proofs address this at several levels. Stealth address protocols allow senders to generate unique one-time addresses for each transaction, breaking the linkability between a blockchain wallet and its transaction history. Privacy-preserving protocols like Tornado Cash (before its legal complications) demonstrated the demand for this and the regulatory complexity it creates.
The more sustainable path is selective disclosure: zk proofs that allow a blockchain wallet owner to prove specific things about their transaction history, that they received a payment, that they hold a minimum balance, that they've never transacted with a sanctioned address without revealing the full history of the digital wallet crypto address to anyone who queries it.
The ability to track blockchain transactions selectively rather than universally is where the privacy design for blockchain wallet infrastructure is heading.
The Regulatory Tension: Privacy vs. Accountability
No serious treatment of zero knowledge proofs and blockchain data privacy can ignore the regulatory dimension because it is where the most significant real-world friction lives.
Regulators, particularly in financial services, have legitimate requirements for transaction visibility. Anti-money laundering frameworks, sanctions compliance, and tax reporting all assume some ability to inspect blockchain transaction data. ZK proofs that make this data opaque to everyone create real compliance problems.
The resolution being worked on across the industry is not "privacy vs. compliance" as a binary choice, but selective disclosure architectures:
- A user can generate a ZKP proving their transactions comply with AML requirements without showing the transactions themselves
- Regulated entities can be granted view keys, the ability to decrypt specific blockchain data for audit purposes without that visibility being public
- Compliance proofs can be submitted to regulators on-chain, satisfying reporting requirements without publishing sensitive data to the world
This is technically achievable. The policy frameworks to govern it are still being written, and the gap between technical capability and regulatory acceptance is significant in most jurisdictions.
If your organisation is navigating compliance requirements for a privacy-preserving blockchain application, our team covers current frameworks and where selective disclosure architectures fit within them. Get started today.
What Gets Stored On-Chain vs. Off-Chain: A Design Decision That Matters
Every team building on blockchain for data applications eventually faces the same architectural question: what actually needs to go on-chain, and what should stay off?
The answer is almost always: less than you think.
On a public blockchain, everything stored on-chain is permanently visible, permanently immutable, and permanently accessible to anyone who queries it. That is valuable for some things - settlement finality, proof of existence, audit trails and actively harmful for others.
The practical framework most well-designed systems use:
- On-chain: Commitments (cryptographic hashes of data), ZK proofs, settlement instructions, access control logic in smart contracts
- Off-chain: The actual sensitive data, encrypted and stored in systems with appropriate access controls — decentralised storage like Filecoin or IPFS, or traditional encrypted databases where regulatory requirements demand it
The crypto ledger records proof of the data's existence and validity. The data itself lives where it can be properly governed. ZK proofs bridge the two, allowing the on-chain system to make verified claims about off-chain data without needing to read it.
This architecture is not a workaround for blockchain's transparency. It is the correct design for any system that handles data with varying sensitivity requirements.
Frequently Asked Questions
Q: What are zero knowledge proofs in simple terms?
A: A zero knowledge proof is a way of proving that a statement is true without revealing any information beyond the truth of the statement itself. In blockchain contexts, this means proving a transaction is valid, a balance is sufficient, or a credential is authentic, without exposing the underlying data.
Q: What is the difference between zk-SNARKs and zk-STARKs?
A: Both are types of ZK proofs used in blockchain systems. zk-SNARKs produce smaller proofs and verify faster but require a trusted setup ceremony. zk-STARKs require no trusted setup and are post-quantum secure, but produce larger proofs. The right choice depends on the specific application's constraints.
Q: How does a blockchain wallet expose user identity?
A: Every blockchain transaction sent or received by a digital wallet crypto address is permanently visible on the public ledger. Over time, transaction patterns, counterparties, and timing can be used to infer identity and behavior even without a name attached to the address. ZK proofs and stealth address protocols are the primary technical mitigations.
Q: Can zero knowledge proofs satisfy regulatory compliance requirements?
A: In principle, yes. Through selective disclosure architectures where ZKP proves compliance without exposing underlying blockchain data. In practice, the regulatory frameworks to formally recognize these proofs are still being developed in most jurisdictions.
Q: What should be stored on-chain versus off-chain for data privacy?
A: On-chain storage should be limited to cryptographic commitments, ZK proofs, and settlement logic. Sensitive data should be stored off-chain, encrypted, with appropriate access controls and linked to the crypto ledger through verifiable proofs rather than direct exposure.
Q: How do ZK rollups relate to zero knowledge proofs?
A: ZK rollups use ZKP to batch thousands of blockchain transactions off-chain, generate a single proof of their collective validity, and post only that proof to the main chain. This achieves significant cost and throughput improvements while inheriting the base layer's security, currently the highest-volume production application of zk proofs in blockchain.
Conclusion
Blockchain data transparency and data privacy are not opposites, they are design parameters that can both be satisfied with the right cryptographic infrastructure. Zero knowledge proofs are the most powerful tool the space has for achieving both simultaneously.
The practical combination of encryption at the data layer and ZKP at the verification layer allows blockchain systems to be auditable without being exposed, verifiable without being readable, and trustworthy without requiring data subjects to surrender control of their information.
This matters beyond finance and crypto. Any domain where sensitive data needs to be verified by parties who should not have unrestricted access to it - healthcare, identity, legal systems, government is a candidate for this architecture.
ZK proofs are not simple to implement. The engineering complexity is real, the tooling is still maturing, and the regulatory frameworks are still catching up. But the direction is clear: privacy-preserving verification on public blockchain infrastructure is not a niche concern. It is what responsible data handling on a public crypto ledger looks like, and increasingly an area where technically specialized teams such as EthElite are helping translate advanced cryptographic design into deployable systems.
Share with your community!