Loading blog post...
How Blockchain Wallets Work: A Technical Guide for Developers and Users
The term 'crypto wallet' is one of the most misleading in the space. It implies storage, a digital purse where coins sit. In reality, a blockchain wallet stores nothing. Your crypto never leaves the blockchain; what a wallet actually stores is the private key that proves your ownership. Understanding this fundamental shift in perspective changes everything about how we secure, build, and interact with the decentralized web
The term "crypto wallet" is one of the most misleading in the space. It implies storage, a digital purse where coins sit. In reality, a blockchain wallet stores nothing. Your crypto never leaves the blockchain. What a wallet stores is the key that proves you own it.
That distinction sounds small. It changes everything about how wallets work, how they fail, and how to think about keeping assets safe whether you are a user holding personal funds or a blockchain developer building applications that interact with wallets.
What a Blockchain Wallet Actually Is
Every address on a blockchain is controlled by a pair of cryptographic keys: a public key (your address, visible to everyone) and a private key (your secret, visible to no one but you).
The public key is like your bank account number, you share it so people can send you funds. The private key is like the PIN that authorises transactions, whoever holds it controls the address.
A cryptocurrency wallet is software or hardware that manages these keys. When you "send crypto," the wallet uses your private key to sign a transaction, a cryptographic signature that proves authorisation without ever exposing the key itself. The blockchain network verifies the signature and updates the ledger.
This is why losing your private key means losing your funds permanently. There is no bank to call, no password reset. The key is the ownership.
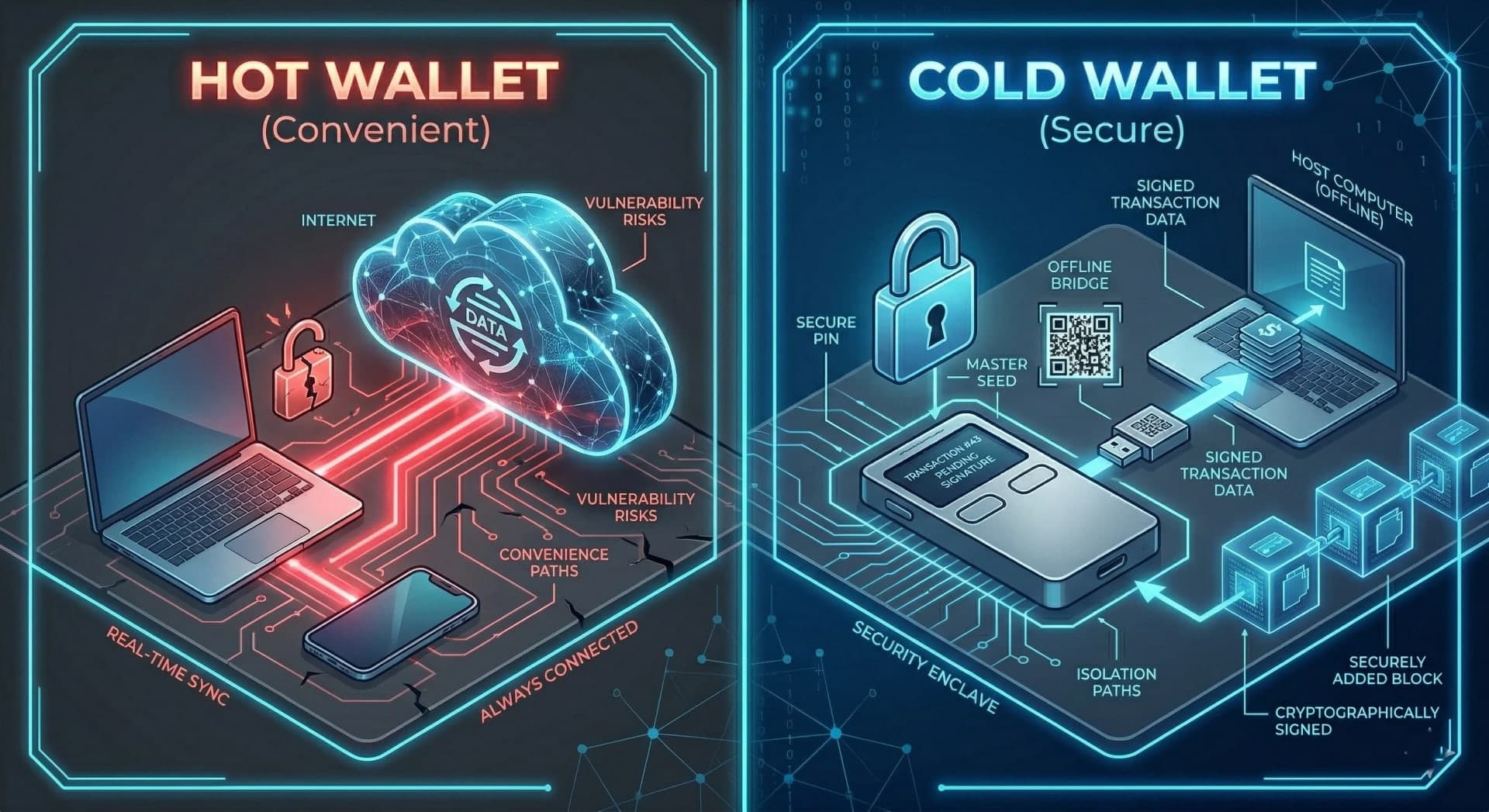
Hot Wallets: Connected, Convenient and Exposed
Crypto wallets that are connected to the internet with browser extensions, mobile apps, desktop applications are called hot wallets. MetaMask, Phantom, and Trust Wallet are the most widely used.
The convenience is real. Hot wallets are free, instant to set up, and integrate directly with web3 applications. For web3 developers building and testing, they are the standard daily tool. For users interacting with DeFi, NFTs or any onchain application, they are the practical entry point.
The risk is equally real. A hot wallet's private key, or the seed phrase that generates it, exists on a device connected to the internet. Malware, phishing attacks, compromised browser extensions, and clipboard hijacking are all live threats. A free crypto wallet in the hot wallet category offers genuine utility and genuine exposure if the device or the user's habits are not secure.
For blockchain developers building wallet integrations, understanding hot wallet security assumptions is essential. Applications that prompt users to sign transactions need to present what is being signed clearly, a significant portion of crypto losses come from users signing malicious transactions they did not fully read.
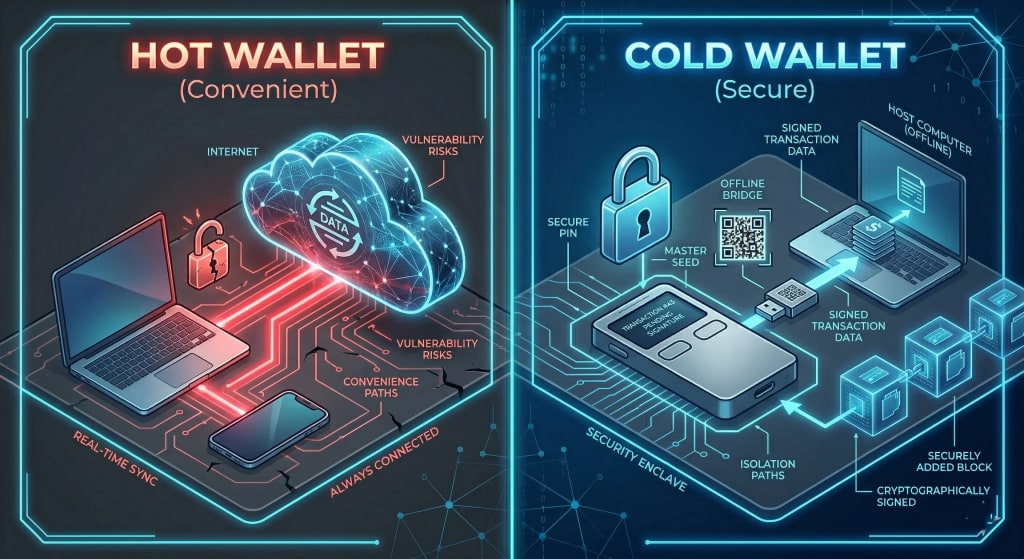
Cold Wallets: The Security Architecture That Actually Protects Keys
A cold wallet keeps the private key on a device that never connects to the internet. The key is generated offline, stored offline, and signs transactions offline. The signed transaction is then broadcast to the network but the key itself never touches a connected environment.
This is the architecture behind the safest crypto wallet setups. The attack surface is dramatically narrowed: remote exploits cannot reach a device that is never online.
Cold wallet crypto setups come in a few forms:
- Hardware wallets — dedicated physical devices (Ledger, Trezor, Coldcard) that store keys in secure elements and sign transactions on-device. The signed transaction passes through a connected computer, but the key never does.
- Air-gapped computers — dedicated machines that have never been connected to the internet, used to generate and store keys for high-value institutional setups
- Paper wallets — private keys printed or written and stored physically. Simple but fragile - no backup, no recovery, and physical theft or damage means permanent loss
For most users, a crypto hardware wallet is the practical sweet spot between security and usability. The best hardware wallet for a given user depends on the chains they use, the assets they hold, and how frequently they transact.
Seed Phrases: The Master Key Behind Every Wallet
Whether hot or cold, almost every modern cryptocurrency wallet uses a seed phrase, a sequence of 12 or 24 words that can regenerate the entire wallet, including all private keys, on any compatible device.
This is both the most powerful and most dangerous feature of modern wallet design.
The power: lose your phone, buy a new one, enter your seed phrase, and every key and address is restored. The hardware wallet gets damaged - enter the seed phrase into a new device. Total recovery from any hardware failure.
The danger: anyone who has your seed phrase has your funds. Not partial access but complete, permanent control. There is no "report stolen seed phrase" mechanism. The words are the keys.
How responsible users and blockchain developers should think about seed phrases:
- Never store a seed phrase digitally. Not in notes apps, not in email drafts, not in cloud storage, not in screenshots
- Physical storage means multiple copies in different physical locations - a single paper backup that burns in a house fire is not a backup
- Metal backup plates (steel seed phrase storage) protect against fire and water in ways paper does not
- For significant holdings, a hardware wallet with its seed phrase stored physically and separately is the minimum reasonable setup
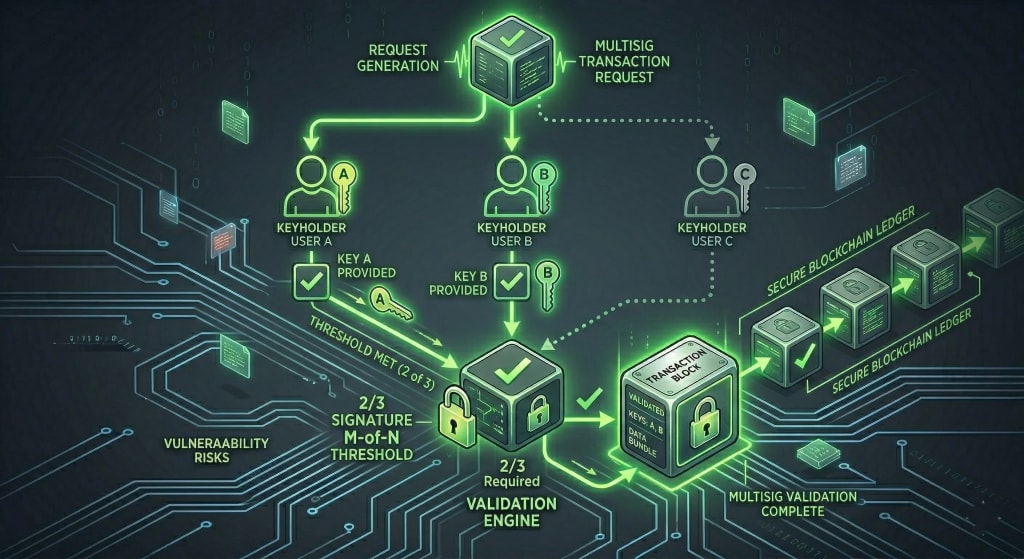
Multisig Wallets: Shared Control for Teams and Protocols
Individual wallets controlled by a single key work for personal use. For teams, protocols, and any treasury holding significant value, a single key is a single point of failure.
Multisig wallets require multiple private keys to authorise a transaction. A 2-of-3 multisig means any two of three keyholders must sign, one compromised key cannot move funds. A 3-of-5 setup means the loss of two keys does not lose the assets.
This is the standard architecture for blockchain development teams managing protocol treasuries, for DAOs controlling collective funds, and for any organisation that needs financial controls analogous to dual-signature banking.
Gnosis Safe (now just Safe) is the dominant multisig implementation on EVM chains. For web3 developers building governance systems or treasury management tools, understanding Safe's architecture, how modules extend functionality, how guards enforce constraints is practically essential.
The security model of a multisig is only as strong as the distribution of its keys. A 3-of-5 multisig where all five keys are on the same person's devices, or where three keys are held by people in the same physical location, does not achieve its security purpose.
What Wallet Standards Matter for Web3 Developers
For web3 development teams building applications that connect to wallets, the technical standards governing those connections are as important as the wallets themselves.
- EIP-1193 defines the JavaScript provider interface — how a browser-based application communicates with an injected wallet like MetaMask. This is the foundation of wallet connection in most web applications.
- WalletConnect is the protocol that enables mobile wallets to connect to desktop applications via QR code or deep link. For applications targeting mobile users or users with hardware wallets that communicate through companion apps, WalletConnect support is effectively required.
- ERC-4337 (Account Abstraction) is the standard that is changing the wallet landscape most significantly. It allows smart contracts to function as wallets — enabling features like gas sponsorship (someone else pays fees for the user), social recovery (losing a key does not mean losing funds permanently), and session keys (authorising a series of transactions without signing each one). For blockchain developers building consumer-facing applications where wallet UX is a barrier to adoption, Account Abstraction is the most important standard to understand right now.
At EthElite, we cover wallet integration patterns and Account Abstraction implementation in more detail. Connect today to get a free consultation and get started.
Choosing the Right Wallet Setup: A Practical Framework
The best crypto wallet setup depends on what you are doing. There is no single answer but there is a sensible framework.
- For daily Web3 use: A reputable hot wallet (MetaMask for EVM chains, Phantom for Solana) for small amounts and frequent interaction. Treat the funds in a hot wallet like cash in a physical wallet, only what you need for daily use.
- For meaningful holdings: A crypto hardware wallet from Ledger or Trezor for assets you are not actively trading. The cold wallet crypto architecture ensures that even a fully compromised computer cannot access funds stored on hardware.
- For serious or institutional holdings: A multisig setup with keys distributed across physical locations and hardware devices. The safest crypto wallet architecture for significant value is not a single device, it is a system designed so that no single failure (device loss, physical theft, death of one keyholder) can result in permanent asset loss.
- For developers: Separate wallets for development, testing, and personal holdings. Never use a wallet holding meaningful funds for testing, mistakes in development are a feature, not a bug, and they should happen in environments where the cost is zero.
Frequently Asked Questions
Q: What is the difference between a hot wallet and a cold wallet?
A: A hot wallet is connected to the internet, convenient but exposed to remote attacks. A cold wallet keeps the private key offline permanently, narrowing the attack surface to physical access only.
Q: What is the safest crypto wallet setup?
A: For significant holdings, a crypto hardware wallet with the seed phrase stored physically and separately. For institutional or team funds, a multisig with keys distributed across multiple devices and locations.
Q: Can I recover my wallet if I lose my hardware device?
A: Yes, as long as you have the seed phrase. Enter it into any compatible wallet and all keys and addresses are restored. Losing the device without the seed phrase means permanent loss.
Q: What is Account Abstraction and why does it matter?
A: ERC-4337 allows smart contracts to act as wallets, enabling features like gas sponsorship, social recovery, and session keys. For blockchain developers building consumer applications, it is the most significant development in wallet UX in years.
Q: What should developers know about wallet security when building Web3 apps?
A: Always display clearly what a transaction will do before asking users to sign. Never request unnecessary permissions. Support hardware wallets through WalletConnect. Understand that users signing malicious or misunderstood transactions is one of the largest sources of crypto loss.
Conclusion
A blockchain wallet is a key manager, not a safe. The assets live on the blockchain. The question is always: who controls the keys?
Understanding this genuinely, not just conceptually changes how both users and blockchain developers think about wallet security. For users, it clarifies what actually needs to be protected (the keys and seed phrase, not the wallet app). For web3 developers, it frames the security responsibilities that come with building applications that interact with user wallets.
The best crypto wallet setup is the one that matches the value being protected with appropriate security architecture. A free crypto wallet hot wallet for small daily use. A crypto hardware wallet for meaningful holdings. A multisig for anything that matters to more than one person.
For teams building wallet-connected products, that same principle extends into how transaction flows, approvals, and signing requests are designed, an area EthElite treats as part of application trust, not just integration.
The technology is accessible. The habits around it determine the outcomes.
Share with your community!