Loading blog post...
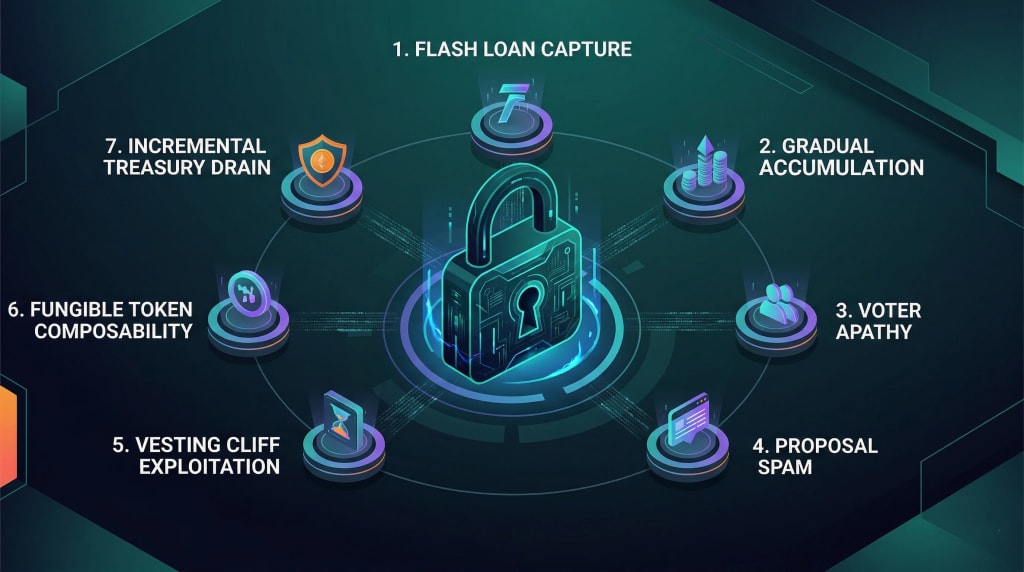
7 Ways Governance Attacks Exploit Weak Tokenomics Design
Most tokenomics documents spend pages on emission schedules and vesting cliffs, but remain silent on a far more expensive risk: deliberate governance sabotage. In the world of DeFi, some of the largest losses in history haven't come from 'bugs', they came from governance systems working exactly as designed, but in the hands of an attacker. From the 13-second 'Flash Loan Capture' to the invisible 'Gradual Accumulation' of power, we break down the seven specific ways weak tokenomics can lead to total protocol collapse and the simple design fixes that can stop them
Most tokenomics documents spend pages on emission schedules and vesting cliffs. Very few spend serious time on what happens when someone deliberately tries to break the governance system.
That omission is expensive. Some of the largest losses in DeFi history came not from smart contract bugs but from governance systems that worked exactly as designed, in the hands of someone who built an attack around them.
Here are seven specific ways it can happen.
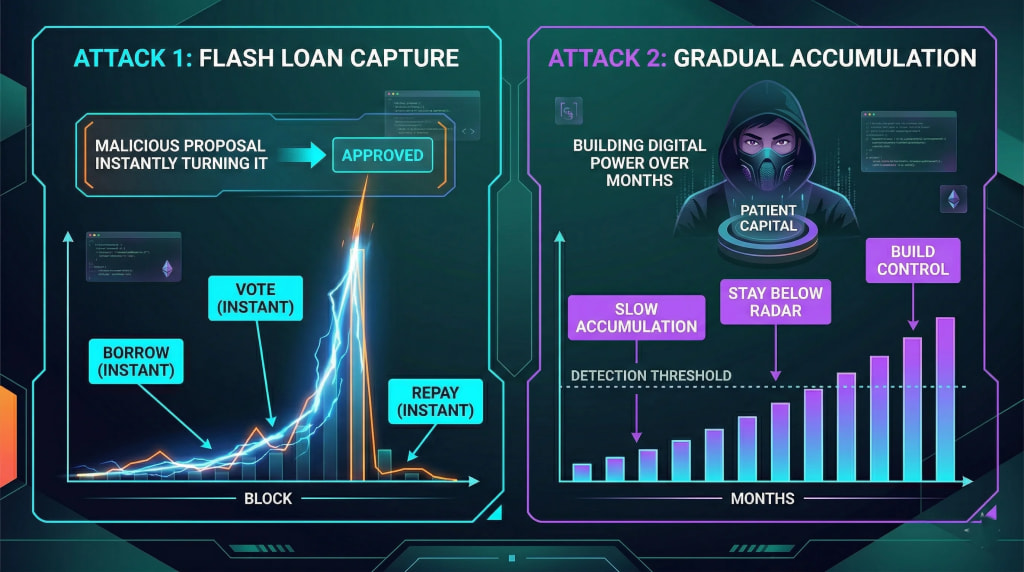
1. Flash Loan Governance Capture: Borrowing a Majority for One Block
This one requires no long-term planning. An attacker borrows a massive amount of the crypto token through a flash loan (a loan that must be repaid within a single transaction) and uses that borrowed voting power to pass a malicious proposal, and repays the loan. Everything happens atomically, in one block.
Beanstalk is the real-world example. In April 2022, an attacker borrowed enough governance tokens to control a supermajority, passed a proposal draining the treasury, and repaid the loan in one transaction. The loss was approximately $182 million.
The tokenomics design flaw: voting power was determined by spot token holdings at the moment of the vote, with no minimum holding period. Flash-borrowed tokens counted identically to tokens held for years.
The fix is simple in principle: require tokens to be locked for a minimum period before they confer voting rights. A borrowed token that arrives and leaves in the same block cannot satisfy a requirement measured in days.
2. Gradual Accumulation: When Patience Is the Attack
Not every governance attack is dramatic. Some are slow and nearly invisible until it is too late.
In a gradual accumulation attack, an adversary buys new tokens steadily over weeks or months, staying below the threshold that would attract attention while building toward control. By the time they have enough to act, the acquisition phase is already over.
Decentralised governance systems are most vulnerable when token distribution is already concentrated, there is no culture of tracking large wallet movements, and the attacker has patient capital and a longer time horizon than the community's attention span.
The response is not purely technical. It requires meaningful quorum requirements, broad delegation infrastructure, and community practices that notice unusual accumulation before it becomes a controlling position.
3. Voter Apathy: When Low Participation Becomes a Weapon
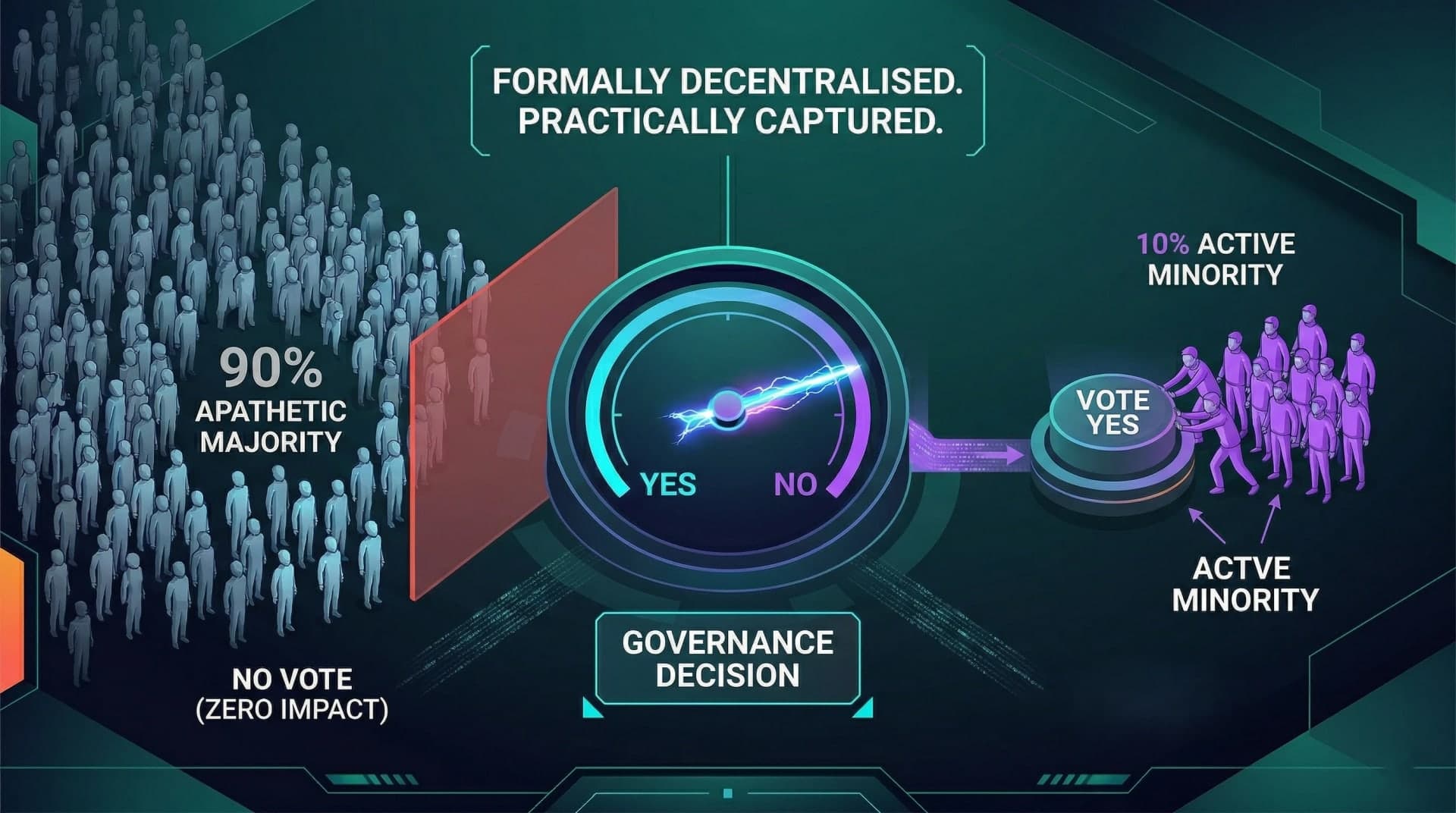
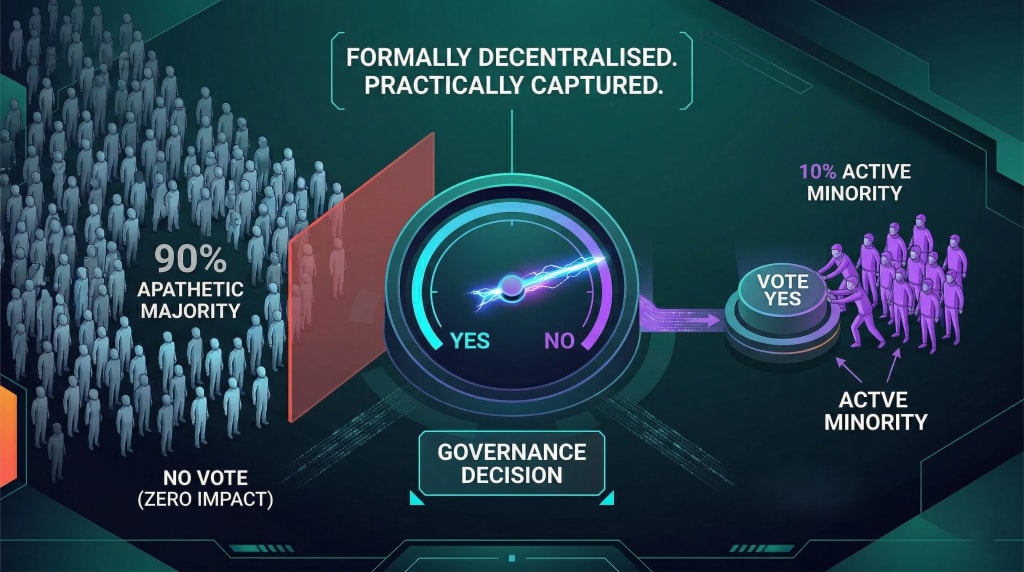
This attack requires no token acquisition at all. It exploits the fact that most token holders simply do not vote.
In most decentralised governance systems, participation rates sit below 10% of eligible tokens. A well-coordinated minority can reliably control outcomes just by showing up consistently while everyone else does not.
Weak tokenomics design amplifies this by concentrating tokens among large holders while distributing the rest to participants with no particular reason to engage. The result is a system that is formally decentralised and practically captured.
Design responses worth knowing:
- Delegation by default — inactive wallets are directed toward active delegates rather than counting as permanent abstentions
- Scaled quorum requirements — routine changes need lower quorum; treasury and protocol decisions need higher ones
- Participation incentives — modest rewards that reduce the cost of engagement without making votes purely transactional
4. Proposal Spam: Drowning Governance in Noise
Governance participation has a real cost: reading proposals, assessing implications, coordinating with others. A sustained campaign of low-quality or distracting proposals exhausts active participants and reduces the quality of attention on legitimate ones.
A well-resourced attacker can generate that cost for the entire community at low expense, waiting for a moment of fatigue to slip through a consequential proposal buried in the noise.
The tokenomics design response: proposal submission thresholds. Without them, anyone can flood the governance queue. With calibrated thresholds, spam becomes expensive for attackers while remaining accessible for genuine participants. Deposit mechanisms where submitters put tokens at risk that are forfeited on frivolous proposals add another layer of friction against abuse.
5. Vesting Cliff Exploitation: Using Unlock Events as Attack Windows
Vesting cliffs create predictable liquidity events like large allocations of new tokens unlocking simultaneously, publicly, on a known date. For patient attackers, these windows are opportunities.
When a large founding or investor allocation unlocks, those tokens typically create selling pressure. An attacker positioned to absorb that supply can achieve governance-significant positions during the resulting volatility, acquiring meaningful voting power precisely when the protocol's early stakeholders are distributing.
Separately, protocols where tokens vest and immediately confer full governance rights create a different version of the same problem. Unlocked tokens that automatically become governance power, regardless of whether the holder has any ongoing stake in the protocol's health, widen the attack surface at precisely predictable moments.
Decentralised governance systems that require a separate staking step to activate voting rights after unlock rather than automatic conversion, hence reducing this exposure significantly.
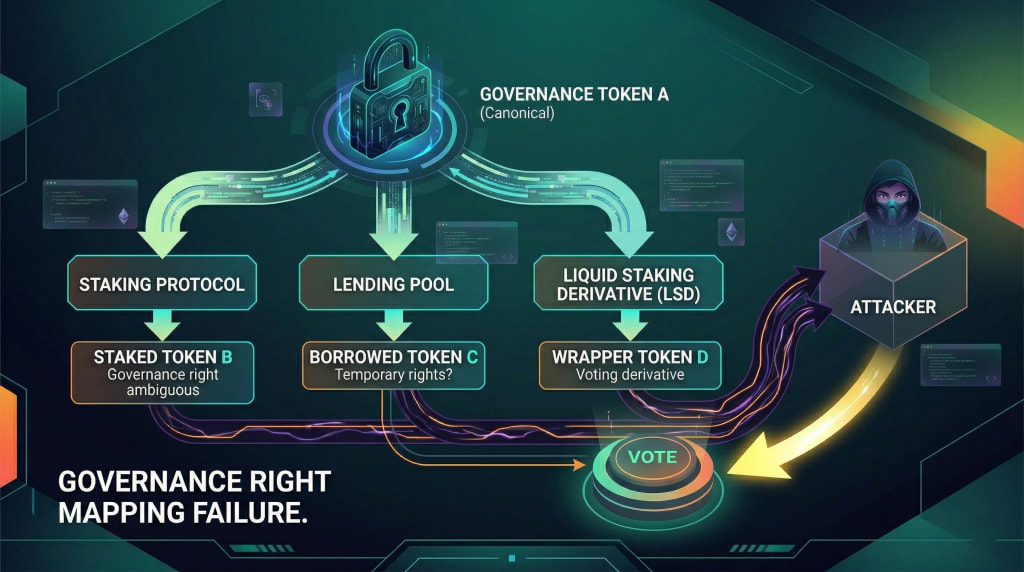
6. Fungible Token Composability: When DeFi Integration Becomes an Attack Surface
Fungible token composability is powerful. It is also a governance attack surface that weak tokenomics design routinely fails to account for.
- The pattern: a governance token that can be borrowed from a lending protocol, used to vote, and returned creates a slower version of a flash loan attack - operating over days or weeks rather than a single block. An attacker borrows governance tokens, influences several proposals, then returns them having never owned a single one. More subtly, protocols that issue derivative tokens for staked governance tokens: liquid staking receipts, wrapped versions create governance token variants that may or may not carry voting rights. That ambiguity is exploitable.
- The design principle: explicit governance rights mapping. The protocol should know precisely which token contracts carry voting rights and participation should require holding the canonical crypto token in a specific verified state: staked, locked, time-weighted, not any derivative that traces back to it.
If you're designing tokenomics for a protocol with DeFi integrations, our Blockchain Development Services includes governance attack surface review as part of the architecture process. Connect today to avail a free consultation.
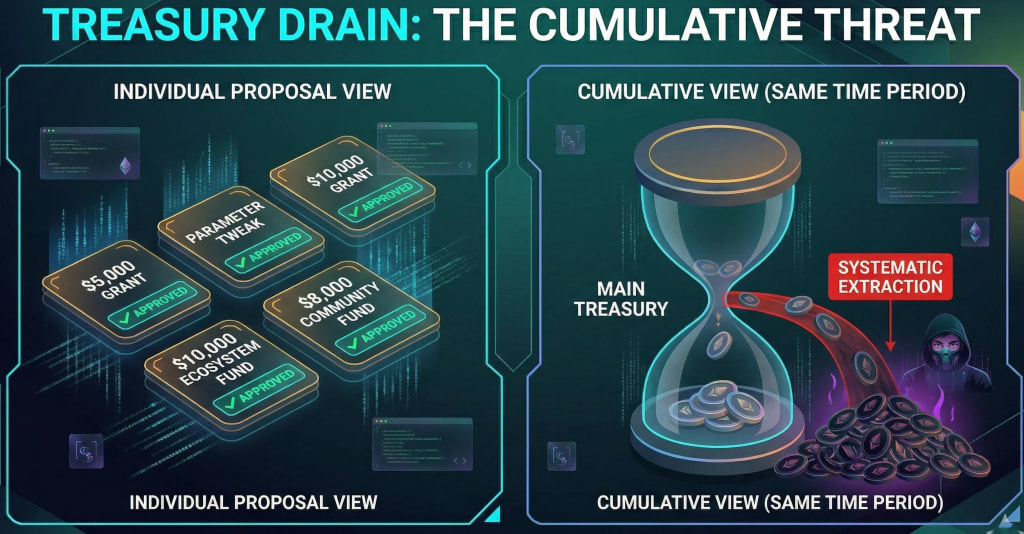
7. Treasury Drain Through Incremental Proposals: Death by a Thousand Votes
Not every attack is a single dramatic drain. Some of the most effective are sequences of individually reasonable-looking proposals that collectively redirect significant value.
An attacker with a persistent governance presence submits a series of grant proposals, parameter changes, or ecosystem fund allocations, each defensible in isolation, collectively representing systematic extraction. This works especially well in decentralisation and local governance contexts where attention is distributed and no one is tracking the cumulative picture.
Each proposal passes because it looks reasonable. The aggregate only becomes visible to someone watching all of them together.
Tokenomics design responses: treasury frameworks with explicit quarterly cumulative limits that require supermajority approval to exceed, and governance dashboards that surface the aggregate picture to all participants, not just the most active.
Separating operational treasury (small allocations, committee approval) from strategic treasury (large allocations, full community vote) matches approval friction to actual stake.
Frequently Asked Questions
Q: What is a governance attack?
A: An attempt to gain illegitimate control over a protocol's decision-making typically by acquiring, borrowing, or exploiting crypto token voting power to pass proposals that benefit the attacker at the protocol's expense.
Q: How do flash loan governance attacks work?
A: An attacker borrows governance tokens within a single transaction, passes a malicious proposal using borrowed voting power, and repays the loan. Minimum token holding periods before voting rights activate are the primary defence.
Q: Why does voter apathy enable governance attacks?
A: Low participation effectively lowers the threshold an attacker needs to reach. A small coordinated group can control outcomes with technically valid vote counts when most token holders never engage.
Q: What tokenomics design changes reduce governance attack risk?
A: Minimum holding periods before voting rights activate, scaled quorum requirements, proposal submission thresholds, and explicit mapping of which token contracts carry governance rights.
Q: What is the difference between formal decentralisation and genuine distributed power?
A: Formal decentralised governance means the mechanism exists. Genuinely distributed power requires active participation and token distribution broad enough that no small group controls outcomes regardless of how the mechanism is designed.
Conclusion
Every attack pattern here exploits the same root failure: tokenomics design that treats governance as an afterthought rather than a security surface.
Flash loan attacks exploit absent holding requirements. Accumulation attacks exploit concentrated distributions. Fatigue attacks find systems without proposal thresholds. Composability attacks find gaps between token derivative rights and governance rights.
Every one of these is preventable with deliberate design, not with complexity, but with the foresight to ask before deployment: how would someone who wanted to break this system go about doing it?
That is where experienced protocol teams add value because governance design only works when voting mechanics, treasury permissions, quorum logic, and execution pathways are tested together, something EthElite typically evaluates before governance goes live.
The protocols that ask that question early spend engineering time on defences. The ones that don't spend it on post-mortems.
Share with your community!