Loading blog post...
Understanding Smart Contract Vulnerabilities and How to Test for Them
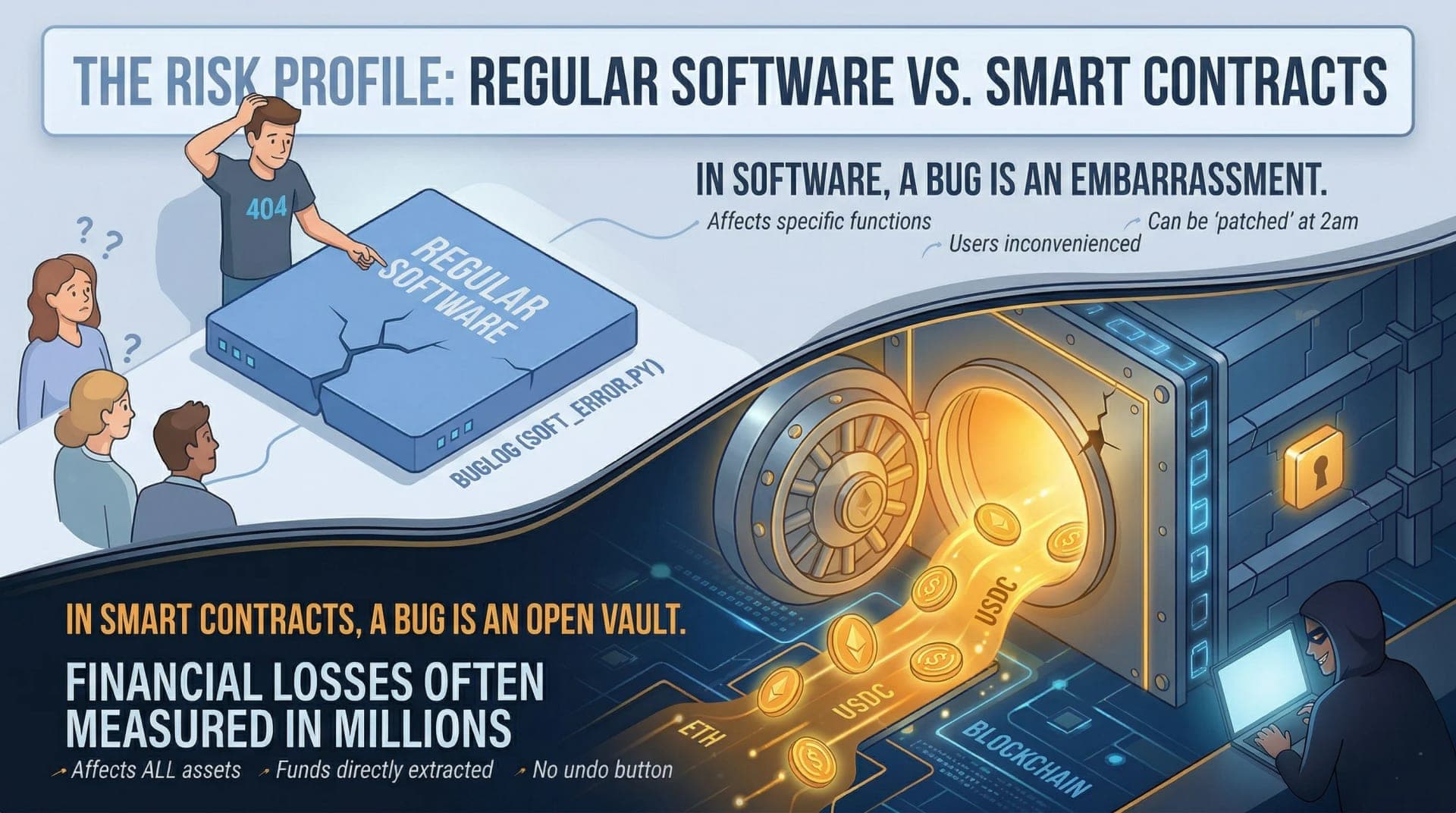
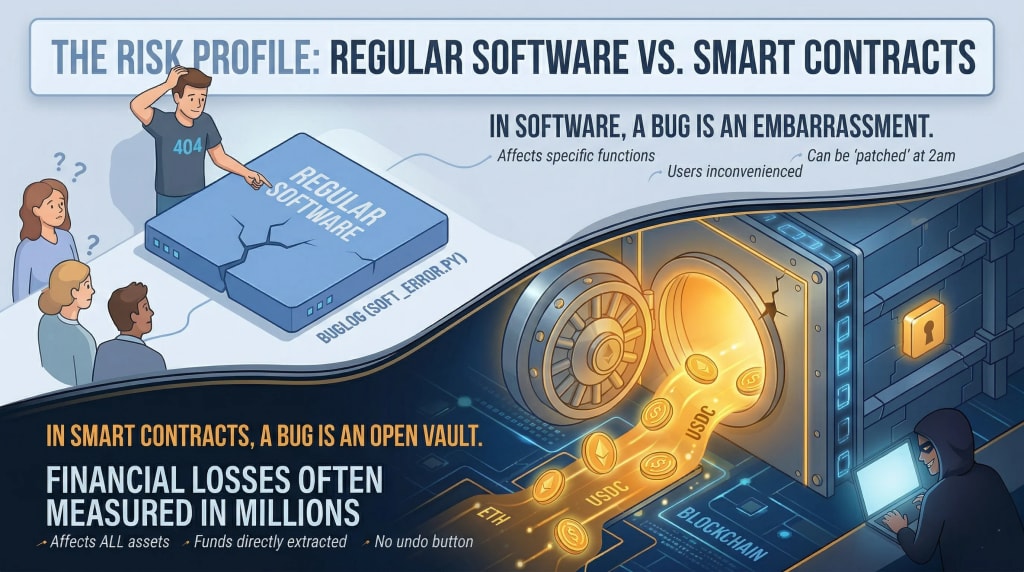
In regular software, a bug is an embarrassment. In a smart contract, it’s an open vault. With billions in TVL at stake, "shipping fast" without adversarial testing is a recipe for disaster. This guide breaks down the critical 2026 vulnerability landscape from cross-contract reentrancy to oracle manipulation and reveals the modern testing stack (Foundry, Fuzzing, and Invariants) used by elite DeFi protocols to secure their code.
In regular software, a bug is an embarrassment. In a smart contract, a bug is a open vault.
Once a smart contract is deployed on a blockchain, it is publicly visible, permanently accessible, and in most cases, irreversible. Anyone in the world can interact with it. If there is a flaw in the logic, someone will find it. And unlike a web app where you can push a patch at 2am, there is no hotfix for a deployed contract. You either built in an upgrade mechanism from the start, or the vulnerability is there until someone exploits it.
That is the threat model every developer working with smart contracts blockchain systems needs to internalize before writing a single line of code.
Why Smart Contract Vulnerabilities Are Different From Regular Software Bugs
Most software bugs cause inconvenience. Smart contract vulnerabilities cause crypto hacks and crypto hacks cause irreversible financial losses measured in millions.
The difference comes down to a few properties unique to blockchain environments:
- Immutability — deployed code cannot be changed. A vulnerability baked into a contract at launch stays there.
- Public visibility — the code is open source by default. Attackers do not need to reverse-engineer anything. They read the same code the developer wrote.
- Immediate financial exposure — contracts hold real assets from the moment they go live. A vulnerability is not a latent risk; it is an active target.
- No intermediary — there is no bank to reverse the transaction, no customer support to call, no fraud department to escalate to.
These are not arguments against using smart contracts blockchain systems, they are arguments for understanding exactly what you are building before deploying it.
The Vulnerabilities That Have Cost the Most And Still Appear in New Code
Smart contract vulnerabilities are not exotic. Most of the biggest crypto hacks in history trace back to a small number of well-understood attack patterns that good testing would have caught. Here are the ones that matter most.
1. Reentrancy
This is the vulnerability that drained The DAO in 2016 - $60 million at the time, the incident that split Ethereum into ETH and ETC. It still appears in audited code today.
Reentrancy happens when a contract sends funds to an external address before updating its own internal state. The receiving address can be a malicious contract that immediately calls back into the original contract which still thinks the original transaction is in progress, so it pays out again. This loop continues until the contract is drained.
The fix is straightforward: update state before making external calls. The Checks-Effects-Interactions pattern exists specifically to enforce this order. The reason reentrancy keeps appearing is that developers reach for intuitive code structure rather than the safe one.
2. Integer Overflow and Underflow
Solidity arithmetic used to have no built-in protection against numbers wrapping around their maximum or minimum values. Add 1 to the maximum uint256 value and you get zero. Subtract 1 from zero and you get the maximum value.
This was exploited in the BeautyChain hack in 2018, where an attacker triggered an overflow in a batch transfer function to mint essentially unlimited tokens.
Solidity 0.8.0 introduced automatic overflow checks, so this is less of a live issue in modern code but contracts written before 0.8 or those using unchecked blocks for gas optimization can still be vulnerable.
3. Access Control Failures
Not every function in a smart contract should be callable by everyone. Functions that mint tokens, upgrade the contract, pause operations, or move funds should be restricted to authorized addresses. Access control failures happen when these restrictions are missing, incorrectly implemented, or accidentally removed during a refactor.
The Poly Network hack in 2021 - $611 million, the largest crypto hack at the time involved an attacker who found a function that could be called by anyone to change the keeper address, effectively handing over control of the protocol's cross-chain messaging.
4. Oracle Manipulation
Many smart contracts depend on external price feeds to make decisions - liquidating positions, pricing trades, calculating collateral ratios. If those price feeds can be manipulated, the contract's behavior can be manipulated.
Flash loan attacks on price oracles work by borrowing a large amount of capital, using it to move the price on a thinly-traded oracle source within a single transaction, triggering the vulnerable contract at the manipulated price, and repaying the loan, all atomically. The attacker returns the capital, but keeps the profit from the manipulated interaction.
Using time-weighted average prices (TWAPs) rather than spot prices, and using decentralized oracle networks like Chainlink rather than on-chain DEX spot prices, significantly reduces this exposure.
5. Logic Errors
The most dangerous vulnerabilities are not the ones with names, they are the ones specific to your contract's business logic. A flaw in how a reward distribution is calculated, a missing validation check in a withdrawal function, an edge case in a multi-step process that only triggers under specific conditions.
Logic errors cannot be caught by generic scanners. They require understanding what the contract is supposed to do and systematically testing whether it does exactly that, nothing more, nothing less.
How to Actually Test Smart Contracts Before Deploying Them
Knowing the vulnerabilities is the first step. Testing for them is where most teams underinvest because testing is slow, expensive, and does not feel as productive as shipping features.
Here is the testing stack that serious teams use.
- Unit testing covers individual functions in isolation. Every function should have tests for its happy path (correct inputs, expected outputs) and its edge cases (zero values, maximum values, boundary conditions). Hardhat and Foundry are the dominant testing frameworks. Foundry's Forge is increasingly preferred for its speed and its native support for fuzz testing.
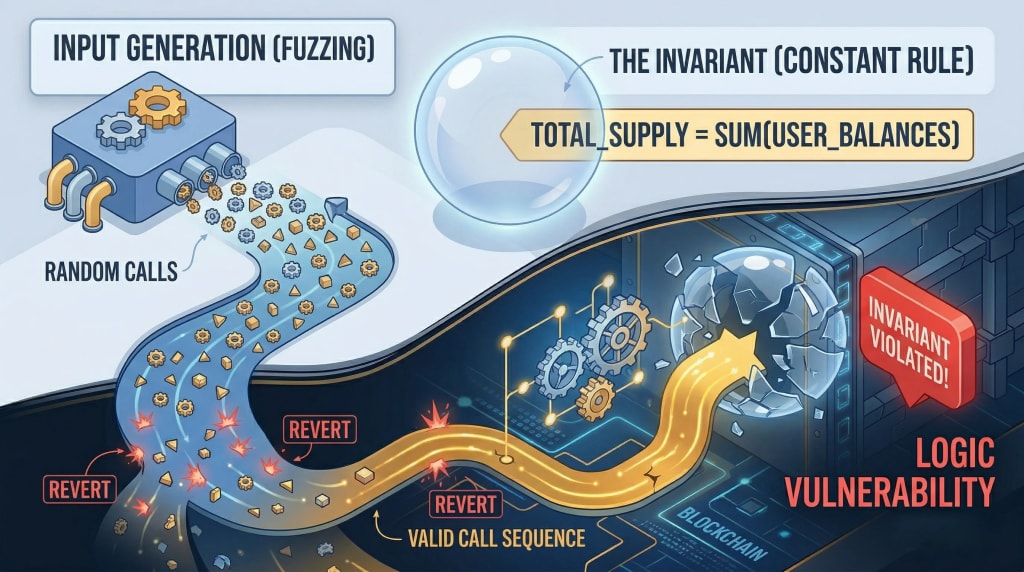
- Fuzz testing generates random inputs automatically and runs them against your contract looking for unexpected behavior reverts where there should not be any, state changes that should not happen, arithmetic that produces impossible values. Foundry's built-in fuzzer has made this accessible to teams that previously would have skipped it.
- Invariant testing is a step further: you define properties that should always be true about your contract's state regardless of what sequence of operations occurs - total supply never exceeds maximum, user balances never exceed total deposits, the sum of all positions never exceeds reserves. The testing framework then tries to find sequences of operations that violate those invariants. This catches logical vulnerabilities that unit tests miss because unit tests only test the paths you thought to write.
- Static analysis tools, Slither being the most widely used can scan your contract code without executing it, flagging known vulnerability patterns. They catch a lot of low-hanging fruit quickly and cheaply. They are not sufficient on their own, but running Slither before any human review is standard practice.
- External audit is not optional for any contract that will hold significant value. Reputable firms bring adversarial expertise that internal teams, no matter how good, cannot fully replicate. An audit is not a guarantee of security; it is a significant reduction in the probability of an undiscovered critical vulnerability.
If you're building a protocol and want to understand where security review fits into the development lifecycle, our Smart Contract Development Services and Smart Contract Audit Service cover how security is integrated from architecture through deployment.
The Testing Mindset: Think Like an Attacker
The most important shift in how good security engineers approach smart contract testing is attitudinal, not technical.
Most developers test to confirm that their code works correctly. Security testing requires asking how the code can be made to behave incorrectly by someone who is actively trying to steal from it.
That means asking questions like:
- What happens if someone calls these functions in an unexpected order?
- What if someone sends a contract address instead of a wallet address as a parameter?
- What can be done with a flash loan and access to this contract?
- If I could call any function multiple times in a single transaction, what could I extract?
- Are there any state transitions that are assumed to be sequential that could be interrupted?
This adversarial thinking is a skill that develops with exposure to post-mortems and with practice. Reading through documented crypto hacks, Rekt News maintains a comprehensive archive is one of the most efficient ways to build pattern recognition for smart contract vulnerabilities without having to learn each lesson from your own deployed code.
Upgradeable Contracts: Security Considerations That Change the Whole Picture
Many production smart contracts use upgrade patterns, proxy contracts that separate the logic from the storage, allowing the logic to be replaced without losing state or requiring migration. This solves the immutability problem but introduces its own security surface.
The main risks with upgradeable smart contracts blockchain deployments:
- Storage collisions — proxy and implementation contracts share storage slots. If the slot layout is not carefully managed across upgrades, data from one variable can corrupt another. OpenZeppelin's upgradeable contract standards exist specifically to handle this safely.
- Uninitialized implementation contracts — the implementation contract behind a proxy should be initialized immediately after deployment. An uninitialized implementation can be taken over by an attacker who calls the initializer first, and if the implementation has a selfdestruct function, the proxy can be bricked.
- Governance of the upgrade key — whoever controls the ability to upgrade the contract controls the protocol. This key is an extreme concentration of power and requires the same security treatment as a treasury key — hardware security modules, multi-sig authorization, timelock delays.
Upgradeability does not make a contract safer. It makes certain kinds of mistakes recoverable at the cost of introducing a different attack surface that requires its own careful management.
After the Audit: Why Security Doesn't End at Deployment
Getting an audit and deploying with a clean report is not the end of security, it is the beginning of the operational security phase.
- Smart contract vulnerabilities can be introduced in updates. An upgrade that passes an audit in isolation can interact with existing state or other protocols in ways that were not anticipated. Every upgrade deserves its own security review, even if it looks small.
- On-chain monitoring is the equivalent of a security camera system for deployed contracts. Tools like Forta, OpenZeppelin Defender, and Tenderly can monitor for unusual transaction patterns, unexpected function calls, large transfers, and other anomalies, alerting the team before a full exploit drains the contract.
- Bug bounty programs turn the global security research community into an extended audit team. A well-designed bug bounty with meaningful rewards for critical findings, Immunefi is the dominant platform in the crypto space provides continuous adversarial review at a cost that scales with what gets found rather than with time spent.
- Incident response planning is the thing almost nobody does until they need it. What is the team's response if a vulnerability is identified? Who has authority to pause the contract? What communication goes out, and when? Who contacts the auditors? Having a documented and rehearsed plan means that if something does go wrong, the response is measured rather than panicked.
Frequently Asked Questions
Q: What is the most common smart contract vulnerability? A: Reentrancy and access control failures remain the most exploited, and both continue to appear in major crypto hacks because small logic mistakes can expose large amounts of value.
Q: Can smart contract vulnerabilities be fixed after deployment? A: Only if the smart contract was built with an upgrade mechanism such as a proxy. Without that, teams usually rely on pausing functions, redeploying, or migrating users.
Q: Is an audit enough to make a smart contract secure? A: No. An audit significantly reduces risk, but secure deployment also depends on internal testing, scenario analysis, and continuous monitoring after launch.
Q: What tools are commonly used to test smart contracts? A: Foundry is widely used for testing, Slither for static analysis, and Hardhat remains common for JavaScript-based workflows. Higher-assurance reviews often add Certora or Echidna.
Q: How do flash loan attacks exploit vulnerabilities? A: Flash loan attacks use temporary capital inside a single transaction to manipulate prices, collateral conditions, or protocol logic before repayment.
Conclusion
Smart contract vulnerabilities remain one of the most immediate risks in blockchain systems, with failures often leading directly to public and irreversible crypto hacks.
The encouraging part is that most major attack patterns - reentrancy, access control flaws, oracle misuse, and logic errors are already well understood and testable.
What consistently separates secure smart contracts from costly failures is process: security built into architecture, development, and review. That is why teams working with EthElite treat security as part of delivery, not something added after code is written.
Share with your community!